
Warping minds since 1983 as an original creative thinker and contributor to cybersecurity, privacy, info warfare, cyber-terrorism, and now: METAWAR.
The Art & Science of Metawar
Orson Welles confirmed the power of immersive storytelling in 1938. Today, audiences beg for ever more immersive experiences.
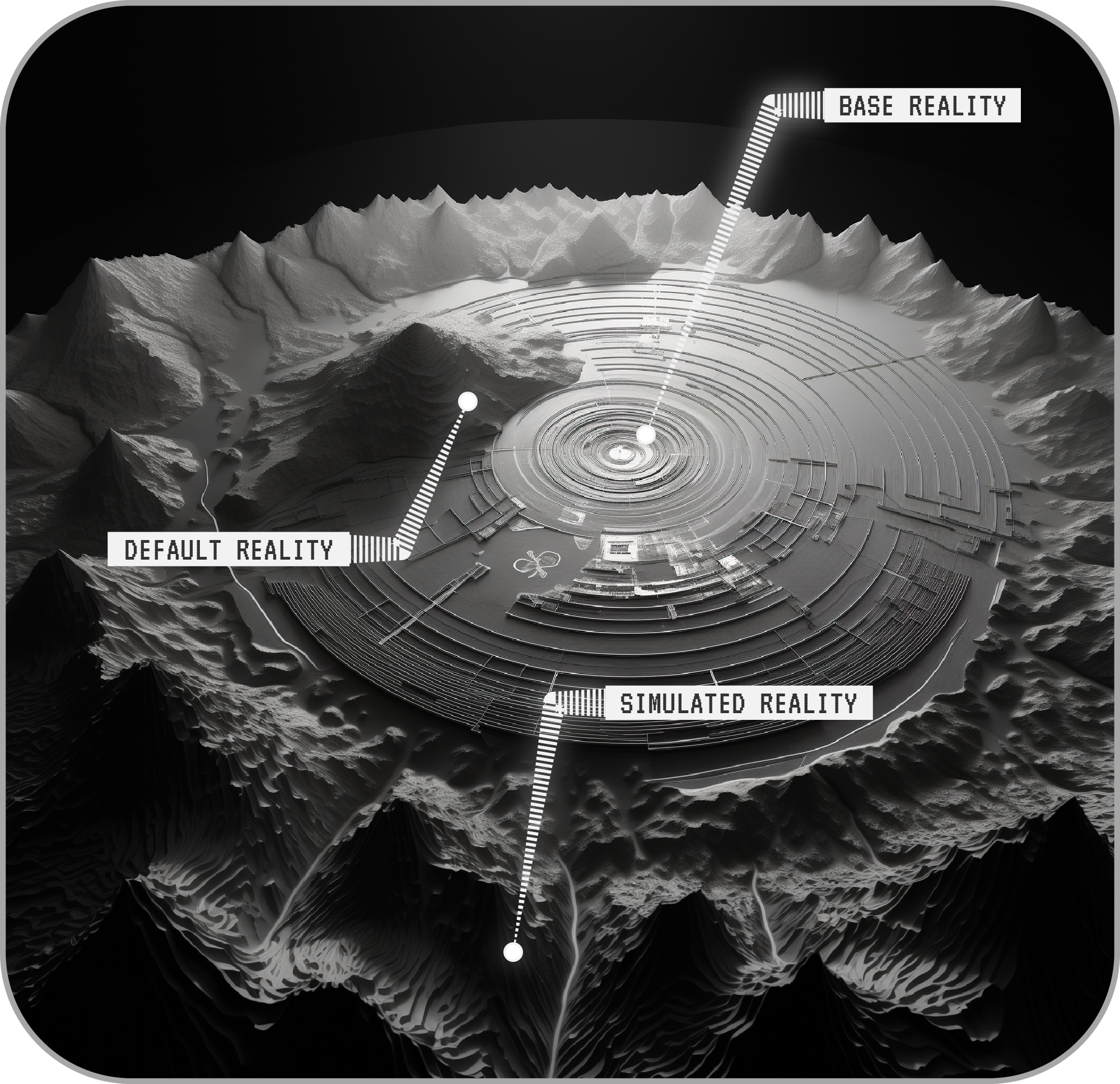
The metaverse is destined to become the most powerful and addictive reality distortion machine ever conceived, and METAWAR is the art and science of that reality distortion.

Where’s Winn?


